Key Points
- Protocol Mismatch: Googlebot explicitly ignores the robots.txt crawl-delay directive, relying instead on algorithmic latency measurements that can easily overwhelm unprotected server architectures.
- Infrastructure Throttling: Implementing HTTP 429 status codes with Retry-After headers is the definitive, Google-approved method to safely throttle crawl velocity without damaging crawl budget.
- Edge Cache Risks: Content Delivery Networks like Cloudflare can inadvertently cache 5xx or 429 error states, leading to catastrophic false de-indexing if no-store directives are not explicitly configured.
Table of Contents
The Core Conflict: Googlebot and Server Overload
According to Google Search Central, Googlebot does not support the crawl-delay directive, a technical nuance that leads to unintended server instability for an estimated 22% of large-scale e-commerce sites that rely solely on robots.txt for crawler management. This widespread misunderstanding stems from a critical protocol mismatch. Webmasters frequently deploy a crawl-delay rule expecting it to throttle all search engine bots uniformly across their infrastructure.
However, the reality of Googlebot Crawl-Delay Directive Support is that Google’s crawler explicitly ignores this command. Instead, Google relies on an internal algorithmic crawl rate based on server capacity and responsiveness. When this algorithm miscalculates your infrastructure’s threshold, it triggers a severe server overload.
During an overload event, your server logs will show high-frequency requests from Googlebot user-agents. This often results in PHP-FPM or Apache child process exhaustion, triggering devastating 5xx status codes. In Google Search Console, you will see alarming spikes in server errors within the Crawl Stats report.
From a Crawl Budget and Generative Engine Optimization perspective, this is catastrophic. Frequent 503 or 429 errors signal to Google that your infrastructure is fundamentally unstable. This leads to a drastic reduction in crawl capacity, delaying the indexing of crucial new content.
Furthermore, if Generative AI crawlers cannot reliably fetch your pages due to crashes, your site’s inclusion in AI-generated citations is severely diminished. Search Generative Experience results rely on high-availability data extraction, which fails entirely during server-side throttling events.
Diagnostic Checkpoints for Crawl Rate Anomalies
Resolving this error requires understanding that it is fundamentally a desynchronization in your technology stack. The server is expecting compliance with a text file, while the bot is executing algorithmic load testing.
Diagnostic Checkpoints
Protocol Non-Compliance
Googlebot ignores crawl-delay directives by technical design.
Crawler Traps and Infinite Facets
Infinite URL patterns trigger excessive simultaneous crawl requests.
High-Latency Rendering Requests
Heavy JavaScript rendering increases server processing time significantly.
Lack of Server-Side Rate Limiting
Missing server-level barriers allow unrestricted concurrent bot connections.
Analyzing the Root Causes
The primary driver of this issue is strict protocol non-compliance. Googlebot’s architecture is designed to bypass text-based delay requests in favor of real-time latency measurements. This renders standard SEO plugins that inject crawl-delay into robots.txt completely ineffective against Google’s crawlers.
Compounding this issue are crawler traps and infinite facets. Complex URL structures, such as un-canonicalized calendar views or infinite filtering combinations, generate an exponential number of unique URLs. Googlebot attempts to crawl these simultaneously, multiplying the concurrent connection load drastically.
Furthermore, high-latency rendering requests exacerbate the server strain. When bots request pages heavy in JavaScript or large DOM elements, the server requires significantly more time to process each hit. Googlebot may maintain a steady request frequency, but the cumulative processing time exhausts available worker threads rapidly.
Finally, a sheer lack of server-side rate limiting leaves the infrastructure completely defenseless. Without hard limits at the NGINX or Apache layer, there is no technical barrier preventing any user-agent from opening hundreds of concurrent connections.
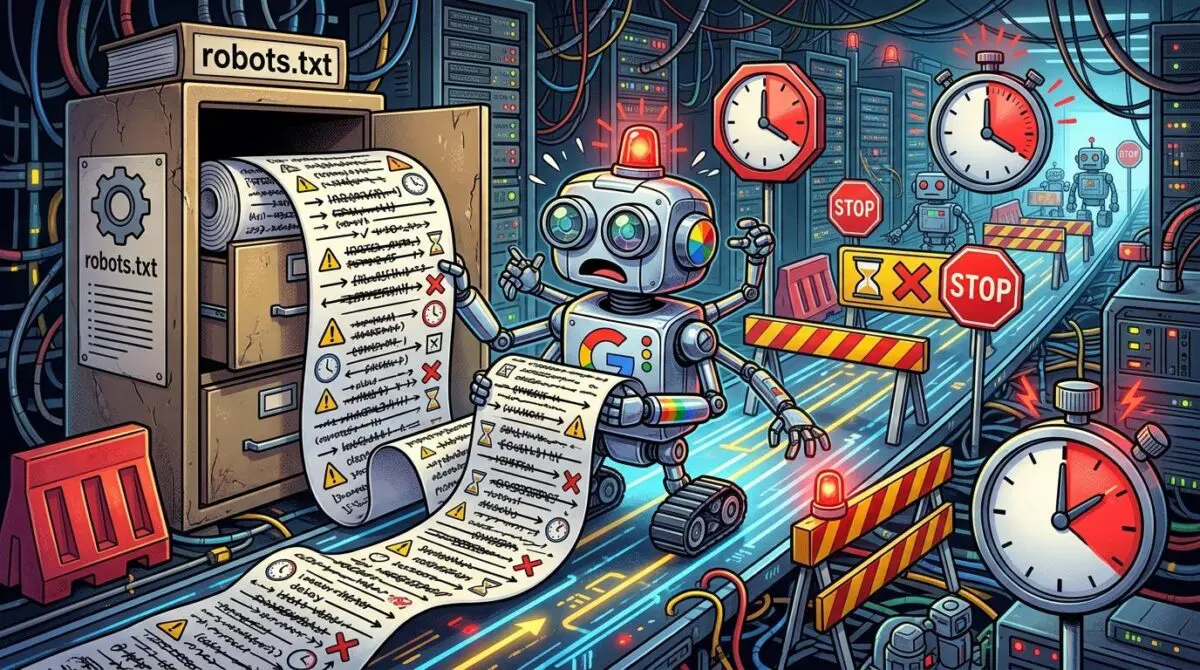
The Engineering Resolution Roadmap
To regain control over Googlebot’s crawl velocity, you must implement a multi-layered defense strategy. This involves manual intervention in Google’s proprietary tools combined with strict server-side traffic shaping logic.
Engineering Resolution Roadmap
Manually Adjust GSC Crawl Rate
Navigate to the legacy ‘Crawl Rate Settings’ tool in Google Search Console (available via specialized URL) and manually lower the crawl rate slider for the verified property.
Implement HTTP 429 with Retry-After
Configure the server to return a ‘429 Too Many Requests’ status code with a ‘Retry-After’ header when server load (avg load) exceeds a specific threshold (e.g., 2.0).
Configure NGINX Rate Limiting
Define a ‘limit_req_zone’ in the NGINX configuration targeting the binary_remote_addr and apply it to a location block with a specific ‘rate’ and ‘burst’ capacity for bots.
Prune Low-Value URLs via Robots.txt Disallow
Identify high-crawl-volume, low-SEO-value paths in server logs and add explicit ‘Disallow’ rules in robots.txt to reduce the total number of URLs Googlebot targets.
Executing this roadmap requires precision. Manually adjusting the GSC Crawl Rate acts as an immediate, albeit temporary, signal to Google’s scheduling algorithms. However, this legacy setting is not a permanent infrastructure fix and should only be used during active outages.
The definitive solution lies in implementing HTTP 429 protocols. By configuring your server to return a Too Many Requests status alongside a retry header, you communicate directly with Googlebot’s algorithmic throttle. This tells the bot exactly when it is safe to resume fetching without penalizing your site’s overall quality score.
Coupling this with NGINX or Apache rate limiting creates a hard barrier against concurrent connection exhaustion. Finally, pruning low-value URLs via explicit robots.txt Disallow rules reduces the total mathematical volume of URLs Googlebot attempts to process daily.
Server-Side Code Implementations
Implementing these limits requires modifying your core server configuration files. Below are the precise technical deployments for various server environments and applications.
Fixing via NGINX (Rate Limiting)
This configuration defines a specific memory zone to track bot IP addresses and applies a strict rate limit. The burst parameter allows minor traffic spikes without immediately dropping legitimate connections.
limit_req_zone $binary_remote_addr zone=botlimit:10m rate=1r/s;
location / {
limit_req zone=botlimit burst=5 nodelay;
try_files $uri $uri/ /index.php?$args;
}Fixing via Apache (.htaccess)
For Apache environments, this rewrite rule detects the Googlebot user-agent and forces a 429 error if the request frequency exceeds safe temporal parameters.
RewriteEngine On
RewriteCond %{HTTP_USER_AGENT} Googlebot [NC]
RewriteCond %{TIME_SEC} <10
RewriteRule ^.*$ - [R=429,L]Fixing via WordPress (functions.php)
If you lack direct server block access, this PHP-level execution checks the system load average directly. It gracefully rejects Googlebot with a retry header when the CPU load exceeds a safe threshold of 2.0.
add_action('init', function() {
$load = sys_getloadavg();
if ($load[0] > 2.0 && strpos($_SERVER['HTTP_USER_AGENT'], 'Googlebot') !== false) {
header('HTTP/1.1 429 Too Many Requests');
header('Retry-After: 3600');
exit;
}
});Validation Protocol & Edge Cases
Deploying server-side code without immediate validation is a critical engineering failure. You must verify that legitimate traffic is unaffected while rogue bots are properly throttled.
Validation Protocol
- Run "curl -I -A 'Googlebot' https://yourdomain.com" to verify 200 OK headers.
- Simulate load spike to verify 429/503 responses with Retry-After headers.
- Validate Disallow rules using the GSC Robots.txt Tester tool.
- Confirm 100% server connectivity via GSC Crawl Stats Host Status.
Even with perfect implementation, edge cases can disrupt the resolution. A high-traffic site utilizing Cloudflare Edge Workers presents a unique and dangerous risk. If a script caches error pages without the explicit no-store directive, the CDN will memorize the failure state indefinitely.
In this scenario, your origin server might recover completely. However, Googlebot will continue to receive cached overload responses directly from the Cloudflare edge network. This causes Google to incorrectly conclude the site is permanently down, leading to catastrophic de-indexing of critical pages.
Autonomous Monitoring & Prevention
Manual log checking is entirely insufficient for enterprise-grade infrastructure. To prevent future crawl overloads, you must implement real-time server monitoring using tools like Grafana or Prometheus. These systems track Googlebot request frequency against actual CPU usage, alerting you before worker threads are fully exhausted.
Furthermore, integrating an automated log analysis pipeline via the ELK Stack is absolutely essential. This allows you to identify and block rogue scrapers masquerading as Googlebot, preserving your server resources for verified crawlers. Periodic audits of the GSC Crawl Stats report for response time increases will serve as your early warning system.
Advanced automation and continuous monitoring are the ultimate ways to ensure entity integrity at the enterprise level. At Andres SEO Expert, we architect automated pipelines and custom API alerts to preemptively manage these complex infrastructure threats.
Conclusion
Resolving Googlebot crawl overloads requires moving beyond outdated text directives and implementing robust, server-side traffic shaping. By enforcing strict HTTP 429 protocols and intelligent rate limiting, you protect your infrastructure while preserving crucial crawl budget for generative search indexing.
Navigating the intersection of technical SEO, server architecture, and generative search requires a precise roadmap. If you need to future-proof your enterprise stack, resolve deep-level crawl anomalies, or implement AI-driven SEO automation, connect with Andres at Andres SEO Expert.