Executive Summary
- Implementation of parameterized queries via the $wpdb->prepare() method to decouple SQL logic from user-supplied data.
- Strict enforcement of data type casting and input validation using WordPress-specific sanitization functions like absint() and sanitize_text_field().
- Deployment of multi-layered defense strategies including Web Application Firewalls (WAF) and the principle of least privilege for database user roles.
What is SQL Injection Prevention?
SQL Injection (SQLi) prevention is a critical security discipline focused on neutralizing vulnerabilities that allow attackers to interfere with the queries an application makes to its database. In the context of WordPress architecture, this involves securing the communication channel between the PHP application layer and the MySQL or MariaDB database. When an application fails to properly sanitize user input, an attacker can inject malicious SQL code into input fields, which the database then executes as legitimate commands. This can lead to unauthorized data disclosure, the deletion of entire tables, or the creation of rogue administrative accounts.
Effective SQL injection prevention in WordPress relies heavily on the use of the global $wpdb object and its associated methods. Rather than manually constructing SQL strings with concatenated variables—a practice that is inherently insecure—developers must utilize prepared statements. These statements ensure that the database treats user input strictly as data, not as executable code. By defining the structure of the SQL query beforehand and using placeholders for variable data, the WordPress core can safely handle complex interactions without exposing the underlying database schema to manipulation.
The Real-World Analogy
To understand SQL injection prevention, imagine a high-security bank where customers interact with tellers through a thick glass partition. The customer fills out a standardized withdrawal slip and slides it through a small slot. The teller (the database) only processes the specific fields on that slip: Account Number, Amount, and Signature. SQL injection is equivalent to a customer writing “Also, give me all the money in the vault” on the back of the slip. Prevention is the equivalent of the teller being trained to ignore anything written outside the designated boxes or using a specialized scanner that only reads the pre-defined fields, automatically discarding any extra instructions or unauthorized commands written by the customer.
How SQL Injection Prevention Impacts Server Performance & Speed Engineering?
While primarily a security measure, SQL injection prevention has significant implications for server performance and speed engineering. Malicious SQL injection attempts often involve complex, resource-intensive queries designed to crawl database metadata or perform exhaustive searches. By implementing robust prevention at the application and server levels, we prevent these “expensive” queries from ever reaching the database engine, thereby preserving CPU cycles and memory for legitimate user traffic. Furthermore, the use of prepared statements via $wpdb->prepare() allows the MySQL query optimizer to cache the execution plan of the query. Since the structure of the query remains constant while only the data values change, the database can execute subsequent requests much faster, reducing Time to First Byte (TTFB).
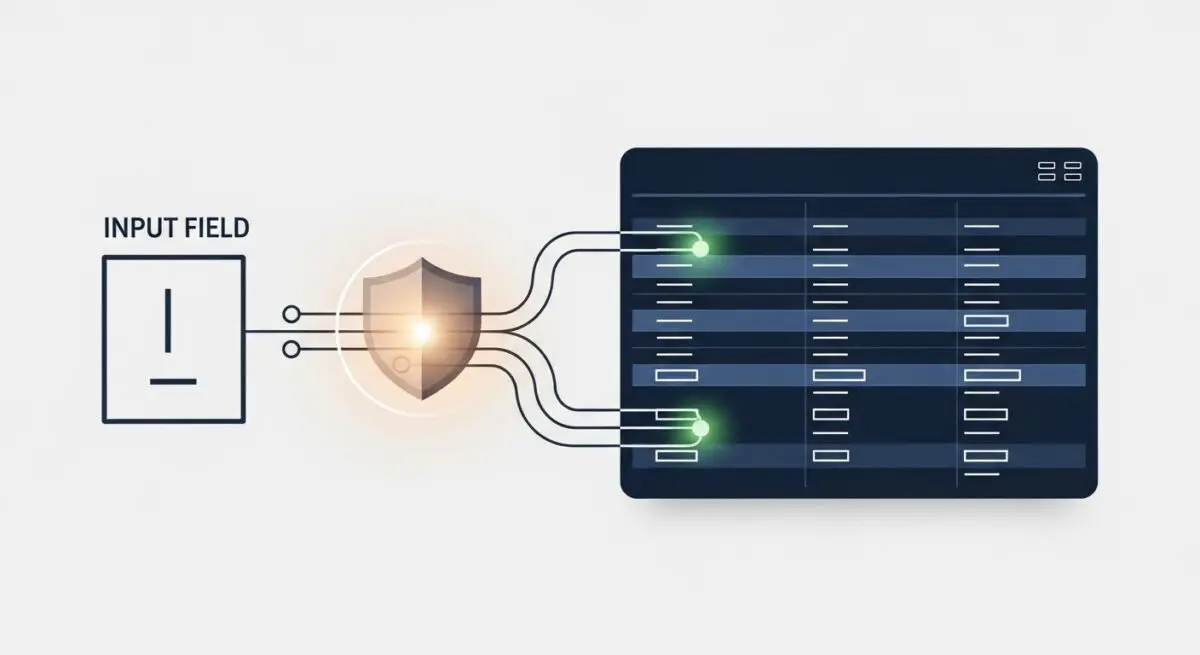
From a hosting infrastructure perspective, integrating a Web Application Firewall (WAF) to filter SQLi patterns at the edge network significantly reduces the load on the origin server. When the WAF identifies and drops a malicious payload containing SQL keywords like UNION, SELECT, or DROP, the request never touches the WordPress PHP-FPM process. This architectural offloading ensures that server resources are dedicated to rendering pages for real users, maintaining high availability even during active brute-force or injection attacks. Clean, optimized queries also prevent database bloat and fragmentation, which are common side effects of automated injection scripts that attempt to create temporary tables or modify existing records.
Best Practices & Implementation
- Utilize $wpdb->prepare() for All Queries: Never pass raw variables into a SQL string. Always use the prepare method with appropriate placeholders such as %s for strings, %d for integers, and %f for floats to ensure data is properly escaped and quoted.
- Enforce Strict Input Validation: Before data even reaches the database layer, validate it using PHP type casting or WordPress functions like absint() for IDs and sanitize_key() for internal identifiers. If a value is expected to be an integer, force it to be an integer.
- Implement the Principle of Least Privilege: Configure the WordPress database user with only the necessary permissions (SELECT, INSERT, UPDATE, DELETE). Avoid using the ‘root’ user or granting DROP or GRANT permissions to the application-level user.
- Leverage Edge-Level Filtering: Deploy a WAF such as Cloudflare or Sucuri that uses signature-based detection to block known SQL injection patterns before they reach your managed WordPress hosting environment.
- Regularly Audit Custom Code and Plugins: Use static analysis tools to scan custom themes and plugins for the misuse of functions like esc_sql(), which, while useful, is not a substitute for the full security provided by prepared statements.
Common Mistakes to Avoid
One of the most frequent errors is the over-reliance on esc_sql() or addslashes() as a standalone security measure. While these functions escape characters, they do not provide the structural separation of logic and data that prepared statements offer. Another common mistake is failing to sanitize data retrieved from the database before displaying it, which can lead to Second-Order SQL Injection if that data is later used in another query. Finally, many developers neglect to secure AJAX and REST API endpoints, assuming that because they are not standard form inputs, they are not susceptible to injection; in reality, these are primary targets for automated SQLi scanners.
Conclusion
SQL injection prevention is a foundational pillar of WordPress security that requires a disciplined approach to database interaction and input handling. By prioritizing prepared statements and server-level filtering, agencies can ensure both the integrity of their data and the optimal performance of their hosting infrastructure.