Executive Summary
- Chmod (Change Mode) is a Unix-level command that defines the read, write, and execute permissions for the owner, group, and public entities.
- In WordPress architecture, precise octal values like 755 for directories and 644 for files are mandatory to prevent unauthorized script execution and data breaches.
- Proper Chmod configuration is a prerequisite for effective Web Application Firewall (WAF) performance and secure PHP-FPM process management.
What is Chmod?
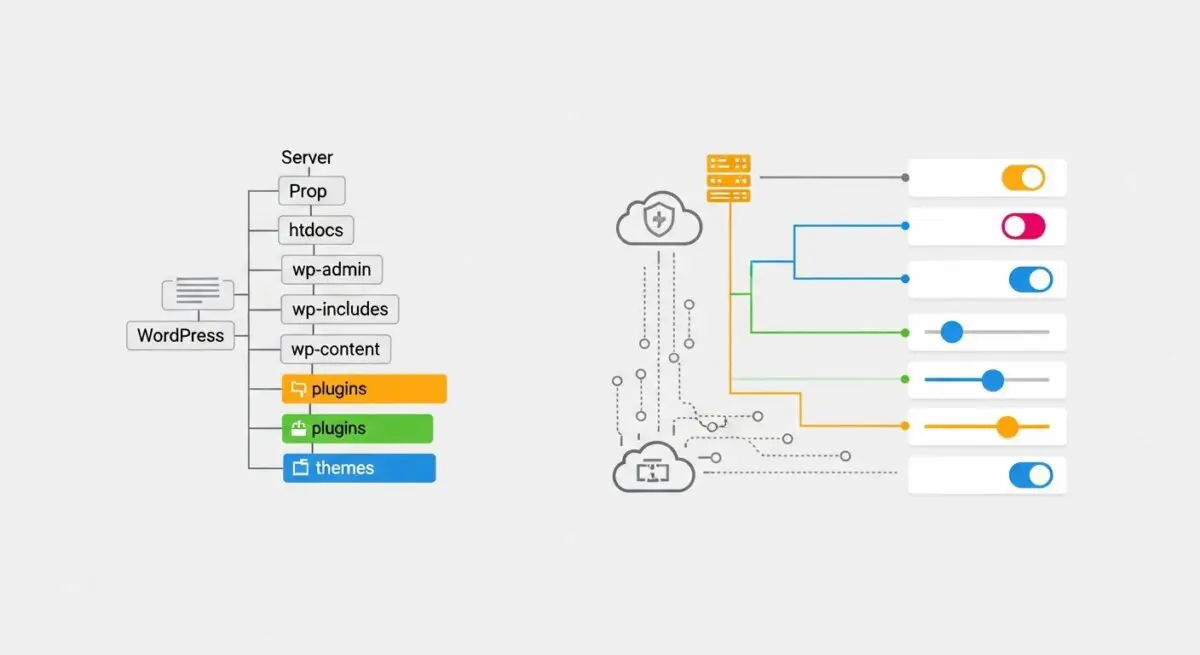
Chmod, an abbreviation for “change mode,” is a fundamental system utility in Unix and Unix-like operating systems used to modify the access permissions of file system objects. In the context of WordPress hosting, which predominantly operates on Linux-based stacks such as LAMP (Linux, Apache, MySQL, PHP) or LEMP (Linux, Nginx, MySQL, PHP), Chmod dictates how the operating system handles requests to interact with the core CMS files, themes, and plugins. These permissions are critical for maintaining the integrity of the WordPress environment, as they define who can read data, modify files, or execute scripts on the server.
Permissions are represented through two primary notations: symbolic and octal. The symbolic notation uses characters (r, w, x) to represent Read, Write, and Execute, while the octal notation uses a three-digit numerical system (e.g., 755 or 644). Each digit in the octal system represents a different class of user: the first digit for the Owner (the user who owns the file), the second for the Group (a collection of users), and the third for Others (the public or world). Understanding these bitwise operations is essential for any Senior WordPress Architect managing high-traffic enterprise environments where security and resource isolation are paramount.
The Real-World Analogy
To understand Chmod, imagine a high-security corporate headquarters. The building has different levels of access controlled by keycards. The building owner (Owner) has a master keycard that allows them to enter any room, move furniture, and start the machinery (Read, Write, Execute). The department employees (Group) have keycards that allow them to enter their specific offices and read documents, but they cannot move the walls or change the locks. Finally, a visitor (Others) might only be allowed to stand in the lobby and look at the directory (Read), but they cannot enter offices or touch the equipment. Chmod is the digital security system that assigns these specific access levels to every single “room” or file within your WordPress installation, ensuring that only authorized “personnel” can make changes to the infrastructure.
How Chmod Impacts Server Performance & Speed Engineering?
While Chmod is primarily a security mechanism, its configuration has significant implications for server performance and speed engineering. In a highly optimized WordPress environment, the PHP-FPM (FastCGI Process Manager) interacts with the file system to execute scripts. If permissions are misconfigured, the server may encounter “Permission Denied” errors, leading to 403 Forbidden status codes and increased server overhead as the system repeatedly attempts to access restricted resources. This creates unnecessary CPU cycles and increases the Time to First Byte (TTFB).
Furthermore, Chmod settings influence how the server handles caching mechanisms. For instance, if the web server (Nginx or Apache) does not have the correct write permissions for the cache directory, static file generation will fail, forcing the server to dynamically generate every page request. This bypasses the performance benefits of edge caching and object caching, leading to a massive degradation in Core Web Vitals. Additionally, modern security architectures involving Web Application Firewalls (WAF) rely on strict file permissions to distinguish between legitimate system processes and malicious script injections. A properly hardened file system via Chmod allows the WAF to operate more efficiently by reducing the attack surface it needs to monitor in real-time.
Best Practices & Implementation
- Standardize Directory Permissions: Ensure all directories within the WordPress root are set to 755. This allows the owner to read, write, and execute, while the group and others can only read and execute, preventing unauthorized directory listing modifications.
- Standardize File Permissions: All WordPress files should be set to 644. This ensures that files are readable by the web server but can only be modified by the file owner, effectively neutralizing many common cross-site scripting (XSS) and injection vectors.
- Harden wp-config.php: As the most sensitive file in the WordPress architecture, wp-config.php should be restricted to 440 or 400. This prevents other users on a shared or VPS environment from reading your database credentials.
- Automate Permission Audits: Use command-line tools like
find . -type d -exec chmod 755 {} +andfind . -type f -exec chmod 644 {} +to recursively apply correct permissions across the entire installation, ensuring no legacy files retain insecure settings. - Restrict the Uploads Directory: While the
wp-content/uploadsfolder requires write permissions (755), ensure that script execution is disabled via .htaccess or Nginx configuration to prevent uploaded malware from running even if Chmod settings are compromised.
Common Mistakes to Avoid
The most frequent and dangerous error made by developers is the use of “777” permissions. Setting a file or folder to 777 means that anyone can read, write, and execute it. This is often used as a “quick fix” for plugin errors or upload issues, but it creates a massive security hole that allows attackers to upload and execute malicious shells. Another common mistake is neglecting the ownership (Chown) of the files. Even with correct Chmod settings, if the web server user (e.g., www-data) does not own the files or belong to the correct group, the WordPress core will be unable to perform updates or save configurations, leading to a broken administrative workflow.
Conclusion
Chmod is a critical pillar of WordPress server-side security and architectural stability. By implementing a strict permission hierarchy, developers ensure that the CMS remains resilient against unauthorized access while maintaining the efficiency required for high-performance web delivery.