Executive Summary
- Implementation of multi-layered filtering across OSI layers 3, 4, and 7 to neutralize volumetric and application-specific threats.
- Utilization of Anycast edge networks to scrub malicious traffic before it reaches the WordPress origin server.
- Critical protection of PHP worker pools and database resources from exhaustion during high-concurrency attack vectors.
What is DDoS Mitigation?
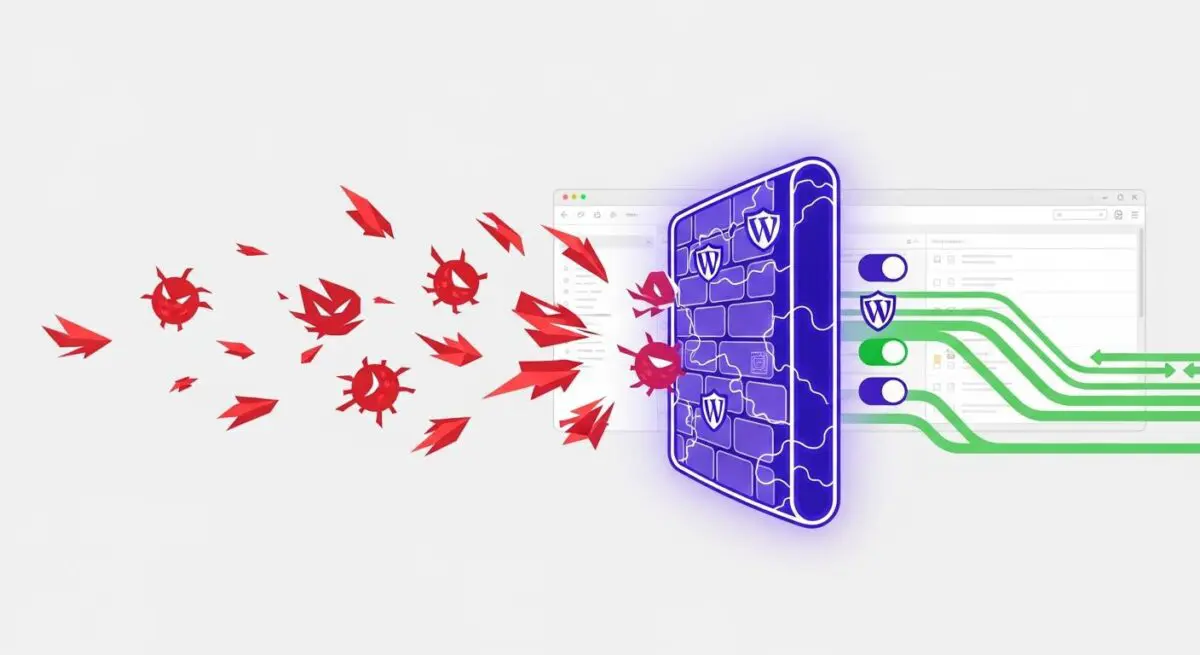
DDoS (Distributed Denial of Service) mitigation refers to the technical process of identifying and neutralizing malicious traffic aimed at overwhelming a WordPress site’s infrastructure. In a WordPress context, these attacks typically target the server’s resources—such as CPU, RAM, and PHP workers—or the database’s connection limits. Mitigation involves a combination of traffic profiling, rate limiting, and signature-based filtering to distinguish between legitimate users and botnets.
Effective mitigation occurs across multiple layers of the Open Systems Interconnection (OSI) model. Layer 3 (Network) and Layer 4 (Transport) mitigation handles volumetric attacks like UDP floods, while Layer 7 (Application) mitigation focuses on sophisticated threats targeting specific WordPress functions, such as the wp-login.php endpoint or the XML-RPC interface. By offloading this filtering to a global edge network, the origin server remains shielded from the computational load of processing malicious requests.
The Real-World Analogy
Imagine a high-end boutique that only allows 10 customers inside at a time. A competitor hires thousands of people to stand in a massive line outside the door, blocking the sidewalk and preventing actual paying customers from even seeing the entrance. DDoS mitigation is like having a specialized security team stationed blocks away at every major intersection. They check every person’s ID and intent before they even reach the street where the boutique is located, ensuring that only genuine shoppers are allowed to proceed while the fake crowd is diverted elsewhere.
How DDoS Mitigation Impacts Server Performance & Speed Engineering?
Without robust mitigation, a WordPress environment is susceptible to resource exhaustion. When an attack hits, the web server (Nginx or Apache) attempts to process every request, quickly consuming available PHP workers. Once these workers are saturated, the server can no longer execute the PHP code required to render WordPress pages, leading to 502 or 504 Gateway Timeout errors. Furthermore, application-layer attacks can trigger intensive database queries, causing high I/O wait times and slowing down the site for legitimate users.
Implementing mitigation at the edge—using a Web Application Firewall (WAF) and Anycast routing—improves speed engineering by ensuring that only “clean” traffic reaches the origin. This preserves the server’s compute power for critical tasks like server-side rendering and REST API processing. Additionally, edge-level mitigation often integrates with Content Delivery Networks (CDNs), which reduces latency by serving cached assets from locations closer to the user, further optimizing Core Web Vitals during periods of high traffic or sustained attacks.
Best Practices & Implementation
- Deploy a Cloud-Based WAF: Utilize services like Cloudflare or Sucuri to intercept traffic at the edge, filtering Layer 7 attacks before they hit the WordPress application.
- Hardening wp-login.php and XML-RPC: Implement strict rate limiting or IP whitelisting for administrative endpoints to prevent brute-force and amplification attacks.
- Origin IP Masking: Ensure the origin server’s IP address is not publicly exposed; use a tunnel or firewall to only accept traffic from the WAF’s IP ranges.
- Configure Failover and Load Balancing: Use high-availability configurations to distribute traffic across multiple server nodes, preventing a single point of failure.
- Monitor Traffic Patterns: Use real-time logging and analytics to identify anomalies in request frequency, allowing for rapid adjustment of security rules.
Common Mistakes to Avoid
A frequent error is relying solely on WordPress security plugins for DDoS protection. While plugins can help with basic hardening, they operate at the application level, meaning the server has already expended resources to process the request. Another mistake is failing to hide the origin IP, which allows attackers to bypass the WAF and attack the server directly. Finally, many organizations neglect to configure custom rate-limiting rules for the WordPress REST API, leaving a significant attack vector open to exploitation.
Conclusion
DDoS mitigation is a fundamental component of enterprise WordPress architecture, ensuring high availability by filtering malicious traffic at the network edge. Proper implementation protects server resources and maintains optimal performance for legitimate users during sophisticated cyberattacks.