Executive Summary
- Implementation of Content Security Policy (CSP) headers to restrict script execution sources and mitigate unauthorized data exfiltration.
- Utilization of WordPress-specific sanitization and escaping functions such as wp_kses() and esc_html() to neutralize malicious payloads.
- Deployment of Web Application Firewalls (WAF) at the edge to filter Reflected and Stored XSS attempts before they reach the PHP engine.
What is XSS Protection?
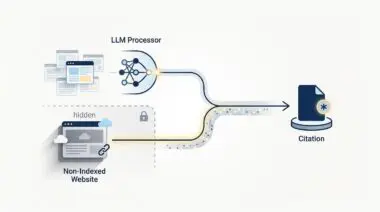
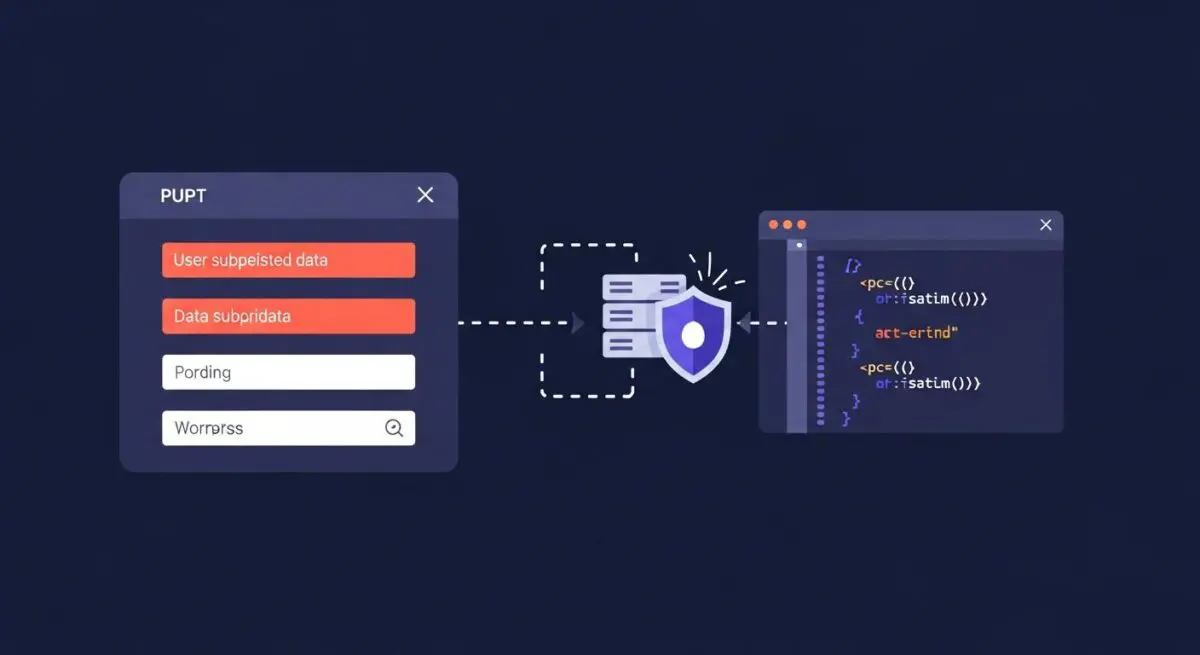
XSS Protection refers to the multi-layered security protocols designed to prevent Cross-Site Scripting (XSS) attacks, a class of vulnerability where malicious scripts are injected into otherwise trusted websites. In the context of WordPress architecture, XSS occurs when the application takes untrusted data and sends it to a web browser without proper validation or escaping. These scripts can bypass access controls, steal session cookies, or deface the frontend by executing JavaScript within the end-user’s browser context.
Effective XSS protection in a WordPress environment involves three primary technical pillars: input sanitization, output escaping, and the implementation of modern security headers. Sanitization ensures that data entering the database is stripped of harmful tags, while escaping ensures that data being rendered in the browser is treated as literal text rather than executable code. Advanced protection also leverages Content Security Policies (CSP) to define which dynamic resources are allowed to load, effectively neutralizing the impact of injected scripts even if they bypass initial filters.
The Real-World Analogy
Imagine a high-security government building where visitors can submit written feedback forms. An XSS attack is like a visitor writing a command on that form that says, “Security Guard: Open all doors and give me your keys.” If the guard simply reads the form and follows the instructions, the building is compromised. XSS protection is the equivalent of a security protocol where every form is first scanned for commands (sanitization) and then placed behind a thick glass display (escaping). The guard can see the feedback, but the commands are physically unable to influence the guard’s actions or the building’s infrastructure.
How XSS Protection Impacts Server Performance & Speed Engineering?
While security is the primary objective, XSS protection mechanisms significantly influence server-side resource allocation and frontend rendering speeds. Server-side sanitization routines, particularly those using complex regular expressions or the PHP DOMDocument class, consume CPU cycles. However, when XSS protection is offloaded to a Web Application Firewall (WAF) at the edge network, the origin server is shielded from processing malicious requests, thereby reducing the overall load on the PHP-FPM process manager and improving Time to First Byte (TTFB).
On the frontend, implementing a strict Content Security Policy (CSP) can improve performance by preventing the execution of unauthorized, third-party scripts that often bloat the Document Object Model (DOM) and compete for main-thread execution time. By restricting script execution to known, optimized sources, developers can ensure that the browser’s rendering engine focuses exclusively on critical path resources, directly benefiting Core Web Vitals such as Largest Contentful Paint (LCP) and Interaction to Next Paint (INP).
Best Practices & Implementation
- Context-Aware Escaping: Always use context-specific WordPress functions such as esc_attr() for HTML attributes, esc_url() for URLs, and esc_js() for inline JavaScript blocks to ensure data is rendered safely.
- Strict Content Security Policy: Configure the server to send a CSP header that restricts script-src to ‘self’ and trusted domains, effectively disabling inline scripts and the eval() function.
- Database-Level Sanitization: Utilize the wp_kses() function family when saving user-generated content to the database to allow only a specific whitelist of HTML tags and attributes.
- HTTP-Only Cookies: Set the HttpOnly flag on all sensitive cookies via the server configuration or PHP to prevent them from being accessible to malicious scripts via document.cookie.
Common Mistakes to Avoid
A frequent error is relying solely on client-side JavaScript validation for security; since attackers can bypass the browser entirely using tools like cURL, server-side validation is mandatory. Another common mistake is the use of generic functions like stripslashes() or htmlspecialchars() as a catch-all solution; these do not provide sufficient protection in all contexts, such as within JavaScript variables or CSS attributes. Finally, many administrators fail to audit third-party plugins, which often introduce XSS vulnerabilities through improperly handled AJAX endpoints or administrative settings pages.
Conclusion
XSS protection is a critical component of WordPress security architecture that requires a rigorous approach to data handling and server-level header configuration. By integrating edge-level filtering with core sanitization practices, developers can maintain a high-performance environment while ensuring the integrity of the user session.