Executive Summary
- The Model Context Protocol (MCP) has shifted API management from human connectivity to governing autonomous AI agents.
- Non-human machine identities now outnumber human employees 80:1, demanding identity-first security platforms.
- By 2027, Agent-to-Agent (A2A) orchestration will require immutable audit trails and token-aware API throttling.
The API security and management landscape has fundamentally fractured. We are no longer living in an era where application programming interfaces are merely technical connectivity utilities. As of mid-2026, APIs have evolved into the strategic control plane of the modern enterprise.
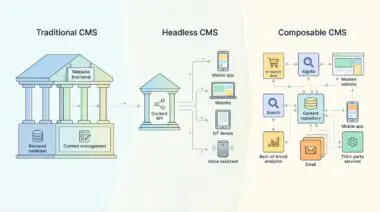
For the better part of a decade, the business world viewed these interfaces simply as digital plumbing. They were the invisible pipes moving data from one application to another. Today, that old paradigm is completely obsolete.
This shift is not just a change in terminology. It represents a massive reallocation of capital and architectural philosophy. The catalyst for this transformation is the explosive rise of Agentic AI.
We are moving rapidly away from legacy perimeter gateways. The smart money is now flowing toward autonomous, identity-first security platforms. These new systems are designed to govern what non-human actors actually do, rather than simply monitoring how they connect.
The Model Context Protocol and the End of the Gateway Era
For years, enterprises struggled with the sheer complexity of connecting fragmented software systems. The traditional approach relied on custom, brittle connectors that required constant maintenance. The Model Context Protocol has effectively solved this integration nightmare.
Before MCP, engineering teams faced the dreaded N by M integration problem. Connecting ten different enterprise applications to ten different language models required one hundred unique, custom-coded integrations. This approach was highly brittle and incredibly expensive to maintain.
MCP has rapidly become the de facto standard for AI-to-enterprise integration. In fact, recent data shows that a staggering 78 percent of enterprise AI teams are now running MCP in production environments. This protocol allows AI agents to securely query proprietary databases through a highly standardized interface.
But this massive leap in connectivity brings an equally massive security challenge. Traditional API gateways were built for human-driven or predictable application traffic. They relied on static rate-limiting and basic perimeter defense models.
Those legacy models completely break down when confronted with autonomous AI agents. Leading platforms are now becoming inherently AI-aware to handle this new reality. Traditional rate-limiting has been replaced by token-aware throttling and dynamic scaling logic.
These advanced systems can adjust throughput based on the intent and reasoning complexity of the calling AI agent. Forward-thinking enterprises like Siemens and Goldman Sachs have already recognized this shift. They have moved past the old API-First mentality to embrace true API-Native architectures.
In these modern environments, every internal capability is treated differently. It becomes a secured, discoverable product interface governed by centralized lifecycle policies. This ensures that innovation does not outpace security.
Follow the Smart Money: Market Disruptors in API Security
The venture capital markets are highly sensitive to architectural shifts of this magnitude. We are seeing a massive influx of funding directed at platforms that can secure the new agentic landscape. Legacy providers are scrambling to acquire these capabilities while nimble startups capture market share.
The leaders in this space are defining an entirely new category known as Agentic Security. They are building the infrastructure that will protect the next generation of enterprise data.
- Salt Security: This pioneer launched the industry-first Agentic Security Platform in early 2026. They introduced the Agentic Security Graph to visualize and protect the complex relationships between large language models, MCP servers, and underlying APIs.
- Wiz: Currently dominating the broader cloud security conversation with a massive valuation exceeding twelve billion dollars. They are leveraging agentless API scanning technology to secure a significant portion of the Fortune 100.
- Exaforce: Recently secured a highly competitive Series B funding round led by former F5 executives. They are building semantic security knowledge graphs that correlate machine identity and API behavior in real-time.
- Oasis Security: Captured immense market attention by raising significant capital to solve the Non-Human Identity crisis. They are providing critical governance in a world where machine identities now outnumber human employees by an incredible eighty to one ratio.
The Silent Crisis of Non-Human Identities
The ratio of machines to humans is perhaps the most alarming statistic for modern security officers. When non-human identities outnumber your human workforce by such a massive margin, identity management must fundamentally change. You can no longer rely on manual provisioning or static access tokens.
Machine identities require dynamic, context-aware credentialing that expires the moment a task is completed. This is why identity-first security platforms are becoming the bedrock of the enterprise control plane. They ensure that an AI agent only has access to the specific data required for its immediate reasoning task.
If an agent attempts to access financial records while tasked with writing a marketing email, the platform instantly severs the connection. This level of granular control is no longer optional. It is an absolute necessity for preventing massive data exfiltration.
Developer Velocity Meets Post-Quantum Defense
While security is paramount, enterprises cannot afford to sacrifice developer velocity. The market is aggressively rewarding platforms that deliver robust security without introducing latency. Developer-led disruptors are proving that you can achieve both speed and safety.
- Zuplo: Emerging as the high-growth challenger to legacy giants like Apigee and Kong. They are managing billions of API calls per month through an edge-native, serverless-first architecture that reduces latency to near-zero.
- Gopher Security: Quietly capturing the high-compliance niche within the fintech and defense sectors. They are providing post-quantum cryptography for MCP connections to bulletproof AI infrastructure against emerging decryption threats.
The rise of post-quantum cryptography in API management is particularly fascinating. Nation-state actors are currently harvesting encrypted enterprise data with the intention of decrypting it once quantum computing matures. By securing MCP connections with post-quantum algorithms today, companies are neutralizing this long-term threat.
It is a brilliant defensive maneuver that is becoming standard practice in highly regulated industries. Executives are realizing that future-proofing their data means protecting it against tomorrow’s computational power.
The Visibility Gap and Hybrid Monetization
Despite these technological advancements, a dangerous perception gap exists in the executive suite. A vast majority of executives believe their existing policies adequately protect their digital assets. However, only a fraction actually have granular visibility into what their AI agents are touching on a daily basis.
This lack of oversight is a recipe for catastrophic data exposure. Platforms like Traceable AI and Cequence are stepping in to bridge this divide. They provide an attacker-lens visibility that actively discovers shadow APIs and zombie endpoints.
Shadow APIs are particularly dangerous in the age of large language models. When an autonomous agent discovers an undocumented endpoint, it can easily bypass established safety filters. This creates a massive blind spot that malicious actors can exploit through indirect prompt injection.
Beyond security, the strategic control plane is also revolutionizing how companies generate revenue. Direct API monetization has matured significantly over the past few years. We are now seeing the widespread adoption of Hybrid Usage Models across the enterprise landscape.
Companies are utilizing platforms like Kong Konnect to implement sophisticated billing infrastructures. These setups mirror the seamless billing experiences pioneered by companies like Stripe. Customers now pay a base subscription fee coupled with token-based overages for heavy AI-driven workloads.
This approach aligns infrastructure costs directly with customer value generation. It also drives incredible operational efficiency across various sectors. For example, modern API stacks in the life sciences sector are drastically reducing validation labor.
Automated, audit-ready compliance workflows are accelerating release cycles and cutting operational overhead by massive margins. This proves that modern API management is as much about revenue enablement as it is about risk mitigation.
Think of legacy API gateways like a medieval castle wall with a single, heavily guarded gate. It works fine when you only have a few merchants entering each day. But Agentic AI is like replacing those merchants with a fleet of autonomous delivery drones flying in every direction. You don’t need a thicker wall; you need a modern air traffic control system. The best API security platforms act as this invisible, hyper-intelligent airspace manager, instantly verifying the identity, flight path, and cargo of every single drone in real-time without slowing them down.
Andres SEO Expert Outlook: The Next 24 Months of API Strategy
As we look toward the horizon, the trajectory of API management is undeniably steep. APIs are no longer an isolated IT concern relegated to the engineering department. They have matured into critical, board-level assets that directly impact corporate valuation.
The stakes have never been higher for enterprise leadership. A single API breach today leaks exponentially more data than the traditional network breaches of the past decade. Consequently, API maturity has become a core metric for assessing organizational trust and determining cyber insurance premiums.
We are also entering an era of severe regulatory hardening. Initiatives like the NIST AI Agent Standards and new federal guidance are forcing a massive operational shift. Enterprises must transition away from trust-based execution models.
The future belongs entirely to policy-based execution. In this new paradigm, every digital action is cryptographically verified and recorded. Compliance will be baked directly into the API control plane rather than treated as an afterthought.
The most exciting frontier, however, is the imminent rise of Agent-to-Agent architecture. By 2027, autonomous multi-agent orchestration will redefine digital commerce. We will see agents from different companies negotiating and executing complex transactions entirely via secured API handshakes.
This will happen without any direct human oversight. To prepare for this agent economy, executives must invest heavily in immutable audit trails and memory lifecycle constraints today. The platforms that facilitate these secure handshakes will become the most valuable infrastructure companies in the world.
The digital landscape is moving faster than ever, and legacy infrastructure simply cannot keep pace. Building a resilient, AI-ready enterprise requires a foundation built on absolute visibility and dynamic governance. Having the right strategic foresight is the only way to turn these technological shifts into a sustainable competitive advantage.
If you are ready to future-proof your business architecture and dominate your market, connect with Andres SEO Expert. We provide the advanced strategies and market intelligence required to keep your enterprise steps ahead of the curve.